But he don't care, 'cuz Johnny was taught
It ain't a crime if ya don't get caught
Apparently this is from 1981's School, Work and Play (World of Tomorrow). I still have my childhood copy of The Usborne Book of the Future: A Trip in Time to the Year 2000 and Beyond which is similar, i.e. somewhat correct about broad trends but amusingly wrong on the specifics, and set in a parallel universe where SPACE: 1999 became real.
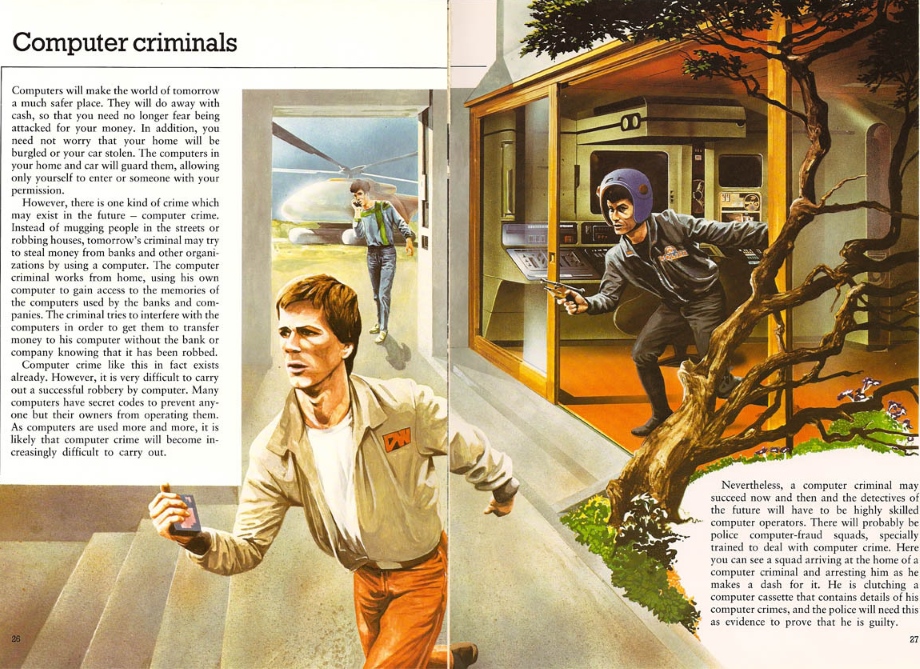
Note the guy in the background: a successful prediction of the modern mobile phone including typical dimensions, microphone / speaker positions, usage stance (implying a unidirectional wind-resistant / noise cancelling mic) and slab form factor with no apparent protruding elements. Pretty good versus the Star Trek: TOS communicator that's generally credited as the first mainstream depiction of the concept. And yet, I think he was only added to cover up the skewed perspective on that cosmic funkadelic helicopter. Presumably he's calling for an ambulance, since the police "special training" was unfortunately in Alvin Stardust impersonation and shooting unarmed, non-violent offenders in the back.
As computers are used more and more, it is likely that computer crime will become increasingly difficult to carry out
has to be one of the most tragically wrong predictions ever. Even large scale, sophisticated attacks don't require much technical skill now, mostly just finding appropriate shady fora so you can become an affiliate for major malware platforms. Everything from means of endpoint exploitation (browser exploit packs), malware R&D, anti-AV packing and obfuscation ("crypters"), C & C / slick statistics reporting and takedown-resistant hosting for same can be provided. This comes at a price of course, starting with your immortal soul because malware has become crystalised evil like encrypting ransomware and "police" lockers that have directly caused suicides.
-
Anti-virus / anti-malware scanners: The first security measure most would name, but actually a tradeoff that can even lead to a compromise, since they are highly privileged processes that have to interact with malicious code. That should mean they are written to a very high standard, but it seems that when any product is seriously investigated areas are found where it just isn't, leading to exploitable flaws. Therefore, install MBAM and remember to actually update/run it periodically, then consider paid AV but if you don't want fine-grained control over how aggressive the heuristic matching is and so on then sticking with the "free" MS Security Essentials or Windows Defender is probably okay. I use Kaspersky AV (not their more complex Internet Security product), mostly on the basis of its cloud reputation mechanism and AV vulnerabilities being high-value thus likely to be reserved for targeted attacks. I'd avoid Sophos because their recent Project Zero report is pretty bad, and it's hard to recommend the market leaders McAfee and Norton since their position means every new malware release is guaranteed to have gone through crypter service permutations until neither detected it.
- Web browser: If you don't have any real preference, use Google Chrome because it's probably the most secure by default (simple but effective sandboxing through a child process with almost no privileges.) The other contenders for that title are recent versions of IE when running in Enhanced Protected Mode and its successor Edge in Win10. I use Firefox because I "need" the configurability, it can be made secure with NoScript and other addons, and Chrome reports certain things you do back to Google for tracking / monetisation purposes. A good ad-blocking extension or builtin facility is ESSENTIAL, not only are parts of the web now borderline unusable without one but "badvert" script injections are the #1 way to send your browser to an exploit kit landing page. Although porn ad networks are the riskiest these occasionally make it into very high-traffic sites, sometimes via them being hacked directly.
-
Additional exploit mitigation: ESSENTIAL and available for free. Malwarebytes Anti-Exploit if user friendliness is paramount, MS EMET for the slightly more technical. (EMET is superior, partly because it covers popular programs other than web browsers, but it's possible to configure sub-optimally. MBAE is browser-only but It Just Works™.)
-
Avoid Adobe software if possible : Especially Flash! 90% of sites now support HTML5 video so you probably don't need it, and due to factors like heavy EK use and the Hacking Team compromise the number of vulnerabilities it's had lately is insane: 13 distinct CVEs in 2015! Annoyingly the IE version of Flash is considered a windows component, it can be removed but you have to take ownership etc which is beyond the scope of this "basic" advice. Uninstall any Flash entries in Programs And Features, then don't use IE and stay on top of Windows Update.
Likewise, unless you use the latest PDF forms or encryption features you probably don't need Adobe Reader / Acrobat. There are free PDF printers and readers that are far more secure. -
Secunia Personal Software Inspector (PSI) : A problem with Windows to date has been its lack of a "package manager" which can update all installed software, despite the fact that packages (MSI/MSU/MSP) have existed since Windows Installer was introduced in Win2000. This should eventually be resolved in Win10, but for now we have a HCI disaster where each program has its own updater service, triggered by its own mysterious conditions, and its own userspace notification process. These fail with their own arcane error codes, which might only be visible if you know how to view its logs, and often use the notification area (aka "system tray") in ways prohibited by MS.
This makes it easy to have vulnerable software installed despite a fixed version being available, which is why exploit kits are so successful. Secunia PSI scans for such installations, and optionally tries to update them. It's a bit clunky: you can get false positives for certain things, and sometimes you have to update them manually. Still, it's a significant improvement over the previous situation.
bob at sdf dash eu dot org